SSO-Driven Assignment of Scoped Views
SSO-driven group assignment allows Scoped Views to be automatically applied to users based on group membership defined in an external identity provider. When a user accesses Ternary through SSO, the platform evaluates group information passed in the IdP token and applies the corresponding Scoped Views without manual intervention.
This mechanism ensures that users consistently receive the correct data access based on organizational roles, both at first login and whenever IdP group membership changes.
SSO must be configured and active for the tenant to enable group-based Scoped View assignment. Group names are matched exactly as received from the IdP.
Prerequisites
Before configuring SSO-driven Scoped Views, ensure the following conditions are met:
- An Admin role is available within the Ternary tenant.
- Scoped Views have already been created and validated for the intended access patterns.
- SSO integration with an identity provider is configured and passing group attributes to Ternary.
Important considerations
The following behaviors are important to understand before using SSO-driven group assignment:
- Group names are case-sensitive and must exactly match the group names sent in the IdP token. If a group already exists in Ternary, creating it again will result in an error.
- Group deletion removes all Scoped Views previously enforced through that group. Users will regain full data access unless restricted by another Scoped View.
- For testing changes, creating a duplicate group instead of modifying an existing production group is recommended.
- Changes take effect immediately. As soon as a user is added to or removed from a group, Scoped View enforcement updates in real time.
- Existing Scoped Views assigned directly to a user are overwritten when a group-based assignment applies.
- Modifying a user’s Scoped View manually after group assignment breaks the association between the user and the SSO-managed group. For example, if a Scoped View was assigned to a user as "Enforced For" and later changed to "Available For" for that user, it will decouple them.
- Group names cannot be edited after creation. To change a group name, create a copy and configure it separately. This is to prevent an issue of an already working Group being modified and breaking the integration.
How are groups configured in Ternary?
To configure a group:
- Navigate to Admin → User Group Configurations.
- Select Add User Group Config.
- Enter the group name exactly as it appears in the IdP token. Remember, it is case sensitive as well.
- Associate one or more Scoped Views that should apply to users in this group.
- Save the configuration.
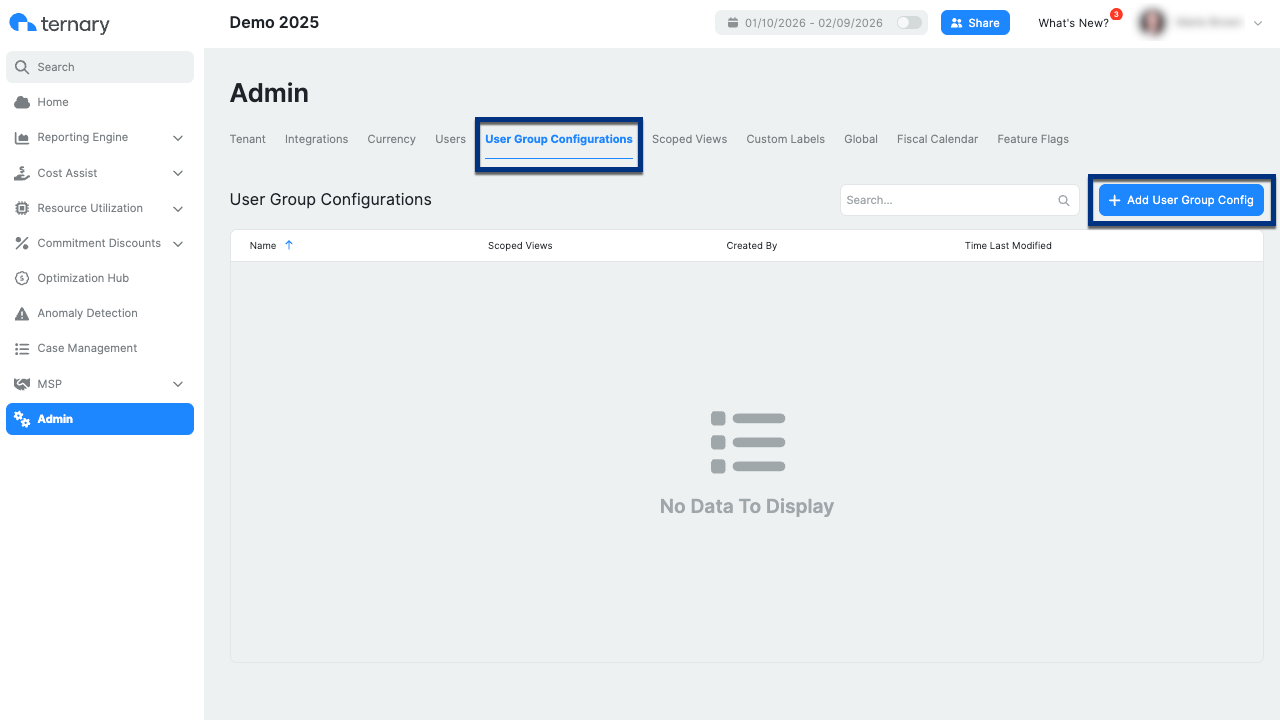
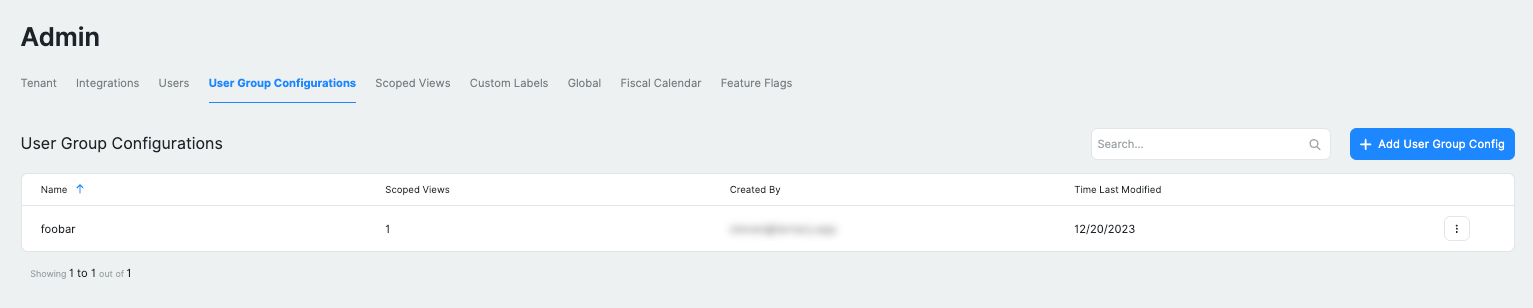
Once created, the group appears in the User Group Configurations table and becomes active immediately. Any user authenticating via SSO with a matching group name will automatically receive the associated Scoped Views.
Updated 4 months ago